Construction
Ensure completing projects on budgets and on time, while ensuring supplier and price management and profitability.
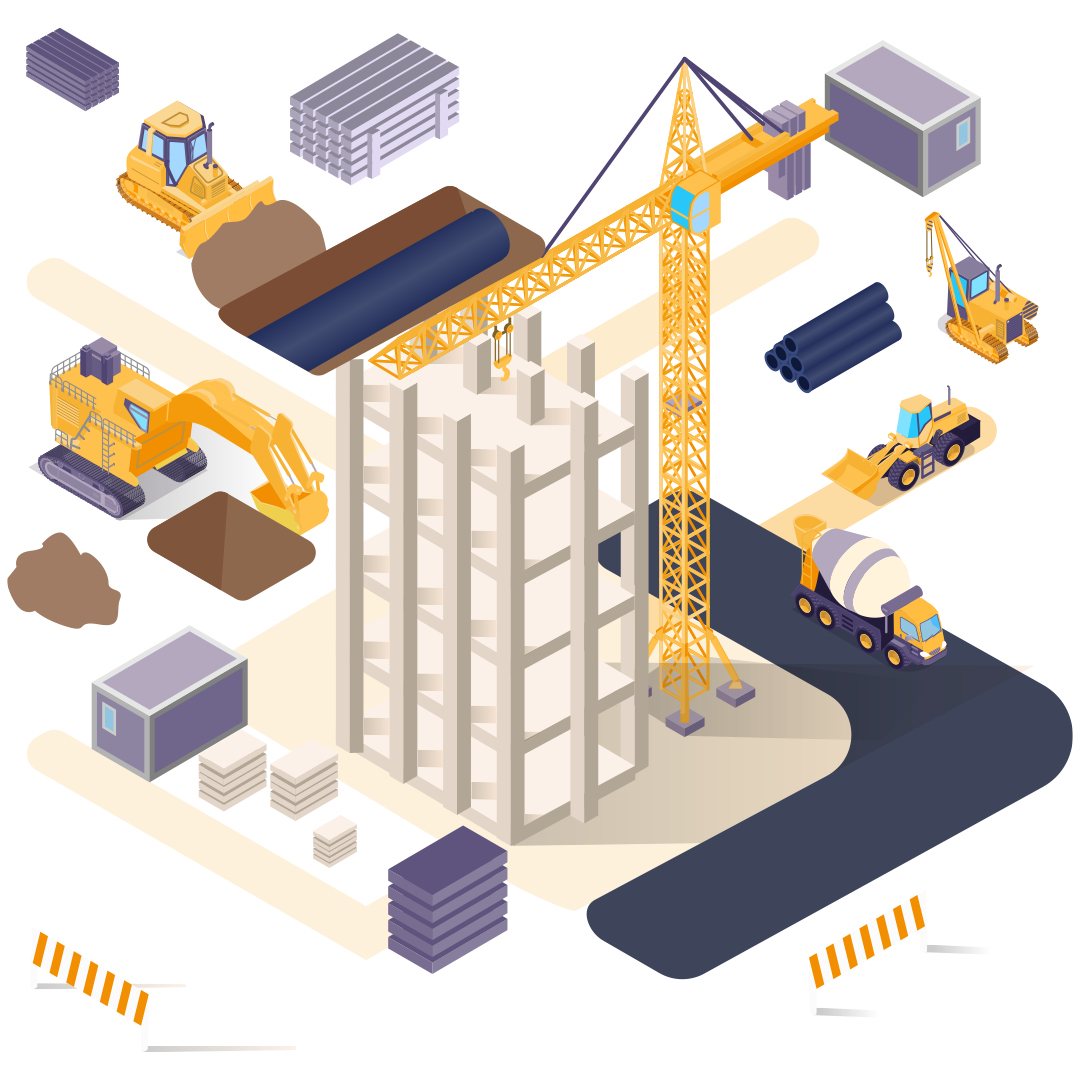
Construction
Ensure completing projects on budgets and on time, while ensuring supplier and price management and profitability.


Financial Management
- Multi-level File Structure
- Pending Inventory Handling & Reporting
- Accounts Receivable & Accounts Payable
- Prepaid & Accrued Expenses
- Check Printing & Bank Transfer Forms
- Financial Statements & Cash Flow
- VAT Settlement & Invoice Bank
- General Ledger

Financial Management

- Multi-level File Structure
- Pending Inventory Handling & Reporting
- Accounts Receivable & Accounts Payable
- Prepaid & Accrued Expenses
- Check Printing & Bank Transfer Forms
- Financial Statements & Cash Flow
- VAT Settlement & Invoice Bank
- General Ledger

Sales & Marketing Management
- Sales Force Management
- Customer Segmentation
- Proforma Invoices
- Price Management
- Analytical Sales Reports
- Customers
- Sales Voucher Integration
- Invoice Settlement
Sales & Marketing Management

- Sales Force Management
- Customer Segmentation
- Proforma Invoices
- Price Management
- Analytical Sales Reports
- Customers
- Sales Voucher Integration
- Invoice Settlement
Purchases, Inventory & Warehouse Management
- Height, Width & Length Item Management
- Barcode Management
- Ending Inventory Evaluation
- Multiple Warehouse Management
- Inventory & Location Management
- Item Segmentation & Reporting
- Multiple Unit Tracking Per Item
- Count & Weight Item Management

Purchases, Inventory & Warehouse Management

- Height, Width & Length Item Management
- Barcode Management
- Ending Inventory Evaluation
- Multiple Warehouse Management
- Inventory & Location Management
- Item Segmentation & Reporting
- Multiple Unit Tracking Per Item
- Count & Weight Item Management
Cyber Security & Access Rights
Securing your data with the best cyber security measures, including role-based access, strong encryption, robust password policies, two-factor authentication and more.

Cyber Security & Access Rights

Securing your data with the best cyber security measures, including role-based access, strong encryption, robust password policies, two-factor authentication and more.

Access Rights Security
Users are organized in a tree fashion similar to that of the company’s administrative tree, and each user can be assigned specific access rights on any option, module and functionality in the system.

Advanced Security
Permitting authorized users’ access in permissible fields and sub-fields. By defining criteria and rules per voucher or record field; providing a high level of user access control.

Station Login Security
In addition, to usernames and passwords, a security option is defined for permitting specific stations to access the system.

Password Security
Controls for assigning password strength and requests to change it periodically.

Login Schedule
Definable time schedules to permit users to log in to the system at specific schedules or times.

Document Printing
User-defined document printing options allowing or denying access to print and post vouchers.

Electronic Signatures
Assigning required signatures for approvals per voucher based on criteria and rules for fields such as voucher amount, branch, department and/or supplier.
Control Dates
User-defined set of controls for data entry security and control. These controls guarantee unintentional data entry that will affect audited or submitted reports.

Two-factor Authentication
A two-factor authentication for additional optional security that sends an SMS to the mobile number defined in the user’s file.

Third Party Login Options
A feature that allows users to incorporate verified third-party applications as a login option to the ERP system.
A Glimpse At Our Partners

Arab Brothers For Precast Industries & Contracting Company Ltd.
General ManagerWe utilize Bisan software in our 3 companies, construction, manufacturing and trading. It is one of the best online accounting applications available, and affordable, it has really improved the workflow among our team, it includes several modules that can cover most of business operations, and can deliver the following values to any business; more ...